What will be returned when the following SQL query is executed? Select driver_no, count(*) as num_deliveries from deliveries group by driver_no having count()>2 O A listing of all drivers who made more than 2 deliveries as well as a count of the number of deliveries A listing of all drivers A listing of the number of deliveries greater than 2 A listing of all drivers who made more than 2 deliveries
Answers
When the following SQL query is executed:
```
SELECT driver_no, COUNT(*) as num_deliveries
FROM deliveries
GROUP BY driver_no
HAVING COUNT(*) > 2
```
The result will be: A listing of all drivers who made more than 2 deliveries as well as a count of the number of deliveries. The query retrieves the driver_no and counts the number of deliveries made by each driver, then groups the results by driver_no. The HAVING clause filters out drivers who made 2 or fewer deliveries, so only drivers with more than 2 deliveries will be listed in the results.
Learn more about SQL here:
https://brainly.com/question/30065294
#SPJ11
When the following SQL query is executed: ```
SELECT driver_no, COUNT(*) as num_deliveries
FROM deliveries
GROUP BY driver_no
HAVING COUNT(*) > 2
```
The result will be: A listing of all drivers who made more than 2 deliveries as well as a count of the number of deliveries. The query retrieves the driver_no and counts the number of deliveries made by each driver, then groups the results by driver_no. The HAVING clause filters out drivers who made 2 or fewer deliveries, so only drivers with more than 2 deliveries will be listed in the results.
Learn more about SQL here:
brainly.com/question/30065294
#SPJ11
Related Questions
Correct all the mistakes in the following sentence:
When you proofread look for punctuation spelling and Capitalization Mistakes.
Answers
Answer:
When you proofread, look for punctuation, spelling, and capitalization mistakes.
Explanation:
Answer:
When you proofread, look for punctuation, spelling, and capitalization mistakes.
:]
Create a for-loop which simplifies the following code segment: penUp(); moveTo(100,120); turnTo(180); penDown(); moveForward(25); penUp(); moveTo(100,120); turnTo(180); penDown(); moveForward(25); penUp(); moveTo(100,120); turnTo(180); penDown(); moveForward(25);
Answers
Answer:
for(var i=0; i<3; i++) {
penUp();
moveTo(100,120);
turnTo(180);
penDown();
moveForward(25);
}
Explanation:
The i variable is the loop dummy. The code block will be executed 3 times.
Create a flowchart that assigns a counselor to a student. You need to ask a student for the first letter of his/her last name. Assign a counselor based on the following criteria:
• A through Mare assigned to Ms. Jones
• N through Z are assigned to Mr. Sanchez
Answers
Answer:
See attachment for flowchart
Explanation:
The explanation is as follows:
Start
Input first_letter (of student's name)
If first_letter is any of N through Z
Assign student to Mr. Sanchez
Else
Assign student to Ms. Jones
Print Counselor
Stop

Which of the addresses below are valid hosts on network 192.168.1.64/26?
Pick two.
a. 192.168.1.88
b. 192.1681.63
c. 192.1681.70
d. 192.1681.95
e. 192.168.1.129
Answers
Given below is the IP address of a network:192.168.1.64/26Now we have to find out which of the given addresses are valid hosts on the above network. A network mask of /26 indicates that 26 bits of the IP address are used for the network portion and the remaining bits are used for the host portion.
The subnet mask for the above network will be:11111111.11111111.11111111.11000000or255.255.255.192We can obtain the number of hosts per subnet using the formula given below:$$\text{Number of Hosts} = 2^{(32-n)} - 2$$Where n is the number of bits used for the network portion. In this case, n = 26. Therefore, the number of hosts per subnet will be:$$\text{Number of Hosts} = 2^{(32-26)} - 2$$$$= 2^6 - 2$$$$= 64 - 2$$$$= 62$$
Now, we can determine the valid hosts in the given network using the following steps:
Step 1: Find the network address by setting all the host bits to 0.$$192.168.1.64/26$$Network address = 192.168.1.64
Step 2: Find the broadcast address by setting all the host bits to 1.$$192.168.1.64/26$$$$= 192.168.1.127$$Broadcast address = 192.168.1.127
Step 3: All IP addresses between the network and broadcast addresses (inclusive) are valid host addresses.
The valid hosts on network 192.168.1.64/26 are:192.168.1.65 to 192.168.1.126Therefore, the two valid hosts from the given list are:192.168.1.70 and 192.168.1.88.
Thus, option C and A are the valid hosts in the network 192.168.1.64/26.
To know more about IP address visit :
https://brainly.com/question/31171474
#SPJ11
The printf method of the System.out object requires at least _______ parameters, unlike print and println, which only require _____ each
Answers
The printf method of the System.out object requires at least one parameter, unlike print and println, which only require zero and one parameters, respectively. The printf method allows you to format output with more control than the other two methods.
When using printf, you can specify the type of output you want to display and format it according to your needs. The first parameter of printf is the format string, which tells the method how to format the output. This string contains placeholders that are replaced with the values you want to display. The placeholders begin with a percent sign (%) followed by a letter that indicates the type of value you are displaying.
After the format string, you can include additional parameters that correspond to the placeholders in the format string. These parameters are separated by commas. The order of the parameters must match the order of the placeholders in the format string.In summary, the printf method of the System.out object requires at least one parameter, which is the format string. The print and println methods only require zero and one parameters, respectively.
To know more about format visit:
https://brainly.com/question/3775758
#SPJ11
you are querying a database that contains data about music. each album is given an id number. you are only interested in data related to the album with id number 3. the album ids are listed in the album id column.you write the following sql query, but it is incorrect. what is wrong with the query?
Answers
The SQL query provided for the question is incorrect. In order to understand the error and to correct it, let's first look at the SQL query provided:
SELECT *FROM music
WHERE album_id = 3;
The above SQL query is incorrect because the query doesn't contain any table name. The table name is missing in the FROM clause. The FROM clause specifies the name of the table from where the data is required. In the given query, only the column name is specified, but the table name is missing.In this situation, the query must have the table name from which we want to retrieve data. Therefore, the correct SQL query for this would be:
SELECT *FROM album
WHERE album_id = 3;
In the above query, we have used the table name as "album" instead of "music". The table "album" contains the data about the album and its properties, which include album_id. So, we use the correct table name, which helps the database to look for the required data in the specified table.
Learn more about SQL here:
https://brainly.com/question/30901861
#SPJ11
on my icomfort thermostat we made it all the way to hook up the wi-fi but it tries but it will not go what do you do
Answers
Make sure your app is up to date and your mobile phone is within 3-5 feet of your thermostat. Restart your mobile device and turn off any apps that may enhance the security, including VPN's, GPS spoofers, etc. These can be turned on again once the connection of the thermostat is complete.
Define wi-fi?A wireless networking technology called Wi-Fi uses radio waves to deliver high-speed Internet access wirelessly. It's a frequent misperception that Wi-Fi stands for "wireless fidelity," although the acronym actually relates to IEEE 802.11x standards.Wi-Fi was the new technology's WECA moniker. (Wi-Fi is not an acronym for "wireless fidelity"; it was developed by a marketing company for WECA and selected for its catchy sound and resemblance to "hi-fi" [high-fidelity].Wi-Fi is more of a facility that provides smartphones, PCs, and other devices within a specific range with wireless Internet connection. On the other hand, computers communicate (send and receive information) through the Internet using the Internet Protocol.To learn more about wi-fi refer to:
https://brainly.com/question/19538224
#SPJ4
3. What will be the output of the following Python code snippet? not(3>4) not(1 & 1) a) True True b) True False c) False True d) False False
Answers
Therefore, the output of the code snippet would be:
a) True True
The correct option is a) True True.
The output of the given Python code snippet can be determined as follows:
1. not(3 > 4):
The condition "3 > 4" evaluates to False. The not operator negates the result, so not(3 > 4) evaluates to True.
2. not(1 & 1):
The bitwise AND operation "1 & 1" evaluates to 1. The not operator negates the result, so not(1 & 1) evaluates to False.
Therefore, the output of the code snippet would be:
a) True True
The correct option is a) True True.
Learn more about Python:https://brainly.com/question/26497128
#SPJ11
Some countries are considering putting something in explosive materials to help track where they came from. What tool would be used to collect the evidence
Answers
Some countries are considering putting Color coded chips in explosive materials to help track them.
What is the tracker?Trace evidence refers to the limited particles, fibers, or residues that maybe transferred all the while the production or handling of explosive matters.
The trace evidence collection kit usually includes parts such as unproductive swabs, tweezers, evidence bags, and vials for continuing and storing the samples. These finishes are used to collect and preserve trace evidence establish surfaces, clothing, and different materials that grant permission have come in trade the explosive material.
Learn more about tracker from
https://brainly.com/question/7791539
#SPJ1
Some countries are considering putting what in explosive materials to help track them? -GPS devices-Computer chips-Color coded chips-Location devices.
help pls lol..
image below

Answers
Answer:
B or C I don't know
so I guessing
Answer:
I think the answer is A
Explanation:
On a recent trip to Disneyworld, Danielle had her picture taken with Minnie Mouse. After the picture was taken, Minnie Mouse signed Danielle's autograph book. Danielle's interaction with Minnie Mouse was actually a service _____ with Disneyworld.
Answers
Danielle's interaction with Minnie Mouse was actually a service provided by Disneyworld.
This service includes the opportunity for guests to have their pictures taken with characters such as Minnie Mouse and have their autograph books signed. These character interactions are an integral part of the Disneyworld experience, adding to the magic and creating memorable moments for visitors.
The service aims to enhance guest satisfaction and create a positive and immersive environment within the park. It is one of the many services offered by Disneyworld to ensure that visitors have a memorable and enjoyable time during their visit.
To Learn more about interaction:
https://brainly.com/question/33403251
#SPJ11
What is another name for a central processing unit?
A. Computer
B. Integrated Circuit
C. Microprocessor
D. Transistor
Answers
The VLOOKUP function looks up values in a table with which feature?
column labels in the top row
column labels in the bottom row
row labels in the leftmost column
row labels in the rightmost column
Answers
The VLOOKUP function looks up values in a table with the feature that allows row labels in the leftmost column. Thus, the correct option for this question is C.
What is the VLOOKUP function?The VLOOKUP function may be characterized as a built-in Excel function that helps you look for a specified value by searching for it vertically across the sheet. This function in Excel may sound complicated, but you will find out that it is a very easy and useful tool once you try it.
The VLOOKUP function lets you search the leftmost column for a value and return another value on the same row in a column you specify. The range of cells in which the VLOOKUP will search for the lookup_value and the return value.
Therefore, row labels in the leftmost column are the feature through which the VLOOKUP function looks up values in a table. Thus, the correct option for this question is C.
To learn more about VLOOKUP function, refer to the link:
https://brainly.com/question/29646445
#SPJ1
Answer:
A -column labels in the top row.
Explanation:
Is the correct answer.
true or false: team members entered into the rfi's responsible party field will receive notification emails regarding the rfi.
Answers
An RFI, or request for information, is a form letter that suppliers must fill out with generic inquiries about their client base and the solutions they offer.
How do you comment to a Procore RFI?
Respond to the Procore RFI
Open your email client and click on the New RFI message.
Click View Online next to More Details. Notes:
Go to the RFI's page's bottom by scrolling. Click Add Response under Activity.
Follow these instructions in the Activity area: Put your comment in the text field.
How should I react to an RFI?
Three steps for responding to an RFI. Use the same strategy you use when responding to other surveys on behalf of your organization when responding to RFI. Check to see if the opportunity is before investing effort to the RFI submission, ensure the correct fit. Evaluate the RFI to learn what this organization is seeking.
To know more about RFI visit:
https://brainly.com/question/29562644
#SPJ4
What five safety habits are you using for the internet?
Answers
Answer: Keep Personal Information Professional and Limited.
Keep Your Privacy Settings On.
Practice Safe Browsing.
Make Sure Your Internet Connection is Secure.
Be Careful What You Download.
Choose Strong Passwords.
Explanation:that’s what is think
T/F low-road transfer occurs most often with novel skills.
Answers
True, low-road transfer occurs most often with novel skills. This type of transfer involves the automatic application of well-practiced skills to new, similar situations without conscious thought, making it more common with novel skills.
True, low-road transfer occurs most often with novel skills. This means that when learning a completely new skill, our brains rely more on basic sensory and motor information and less on higher-level cognitive processes. This type of transfer occurs when the underlying neural pathways and structures are similar between the learned and new skill. However, it's important to note that the amount of content loaded in the original skill can also affect transfer. The more complex and varied the original skill, the more likely it is that high-road transfer (involving higher-level cognitive processes) will occur.Low road transfer occurs when the initial learning task and the transfer task are sufficiently similar in context and conditions so there is a high level of automaticity. High road transfer requires being able to identify mindful abstractions and connections from the initial learning task and the transfer task.
learn more about low-road here:
https://brainly.com/question/6792613
#SPJ11
Which line of the function has an error? int computesumofsquares(int num1, int num2) { int sum; // line 1 sum = (num1 * num1) (num2 * num2); // line 2 return; // line 3 }
Answers
The line of the function that has an error is (num1 * num1) and (num2 * num2)
Which line of the function?The mistake is in 2 of the function. The multiplication movement betwixt (num1 * num1) and (num2 * num2) should be recouped accompanying an adding operation to estimate the total of squares right.
The corrected line 2 bear express: scsssum = (num1 * num1) + (num2 * num2);Additionally, the return assertion following 3 bear specify the changeable reach be returned, in this manner:bashreturn total;
Learn more about error from
https://brainly.com/question/30062195
#SPJ1
what is the function of filters?
a. forwarding mails
b. compose mails
c. block mails
d. send mails
Answers
Forwarding mails is the function of filters.
Thus, Electronic mail, or simply "email," is a form of communication that employs electronic devices to send messages via computer networks. The term "email" can apply to both the method of delivery and the specific messages that are sent and received.
Since Ray Tomlinson, a programmer, invented a mechanism to send messages between computers on the Advanced Research Projects Agency Network (ARPANET) in the 1970s, email has existed in some form.
With the introduction of email client software (like Outlook) and web browsers, which allow users to send and receive messages via web-based email clients, modern versions of email have been widely accessible to the general public.
Thus, Forwarding mails is the function of filters.
Learn more about Emails, refer to the link:
https://brainly.com/question/16557676
#SPJ1
Rachel wants to minimize project risks. Arrange the steps in an order that will correctly help Rachel and her team to minimize project risks.

Answers
Answer:
identify, evaluate, prioritize, and then control
Explanation: I got a 100% on my test.
What's not an computer characteristic ??
Answers
Answer:
A computer is an electrical machine
The computer cannot think at its own
The computer processes information error-free
The computer can hold data for any length of time
Explanation:
The computer is an electrical machine is not a computer characteristic option (A) a computer characteristic is correct.
What is a computer?A computer is a digital electronic appliance that may be programmed to automatically perform a series of logical or mathematical operations. Programs are generic sequences of operations that can be carried out by modern computers. These apps give computers the capacity to carry out a broad range of tasks.
The question is incomplete.
The complete question is:
What's not a computer characteristic?
A computer is an electrical machineThe computer cannot think on its ownThe computer processes information error-freeThe computer can hold data for any length of timeAs we know,
The characteristics of a computer are:
The computer is unable to think for itself.
Information is processed by the computer without error.
The computer has unlimited storage capacity for data.
Thus, the computer is an electrical machine is not a computer characteristic option (A) a computer characteristic is correct.
Learn more about computers here:
https://brainly.com/question/21080395
#SPJ2
How do I fix TypeError int object is not Subscriptable in Python?
Answers
You must change the integer to an iterable data type, such as a string, in order to correct this problem. And if you converted something to an integer and now you're getting the error, you need to change it back.
The object is not subscriptable type error; what should I do?Convert the unordered set to an ordered list or tuple before accessing it in order to resolve the TypeError:'set' object is not subscriptable, or eliminate the indexing or slicing function altogether.
What Python objects are subscriptable?Subscriptable objects are, to put it simply, things that can be subscripted. In Python, subscriptable objects include strings, lists, tuples, and dictionaries. Python implements array if we use the syntax array[0].
To know more about data visit:-
https://brainly.com/question/13650923
#SPJ4
write a short note on folder
Answers
Answer:
A short note on folder
A folder that is used in computers with the virtual location for applications,documents, or the other sub-folders .
Folders help in storing and organizing files and data in a computer .
I hope this might help u
Takes a 3-letter String parameter. Returns true if the second and
third characters are “ix”
Python and using function
Answers
Answer:
def ix(s):
return s[1:3]=="ix"
Explanation:
Explain any TWO (2) data information that shall be covered under "Safety Data Sheet" and elaborate why do you think the information is needed
Answers
Safety data sheets include details about chemical items that assist users in evaluating the risks. They outline the risks the chemical poses and include details on handling, storage, and emergency procedures in the event of an accident.
The properties of each chemical, its physical, health and environmental properties, protective measures, and precautions for handling, storage and transportation of the chemical are contained in a safety data sheet (formerly called safety data sheet).
Provides recommendations for each individual chemical on topics such as:
PPE, or personal protective equipmentfirst aid techniquescleanup procedures for spillsTo learn more on Safety Data Sheets, here:
https://brainly.com/question/28244620
#SPJ4
Classification, affinity grouping, and estimation are______methods used by managers to make their data more meaningful.
Answers
which of the following is not a component of URL; a. web protocol b. name of browser c. name of web server d. name of the file with the directory
Answers
The component of URL that is not listed correctly is b. name of browser. The components of a URL (Uniform Resource Locator) are:
a. Web protocol: specifies the protocol used to access the resource, such as HTTP or HTTPS.
b. Domain name or IP address of the web server: identifies the location of the server hosting the resource.
c. Path to the resource: specifies the location of the specific resource on the server, including the name of the file and any directories or subdirectories.
d. Query parameters (optional): additional information that is sent to the server to help retrieve or filter the resource.
The name of the browser is not a component of the URL itself, but rather a software application that is used to access the URL.
What is the minimum number of connections that must be broken or removed in the network before computer E can no longer communicate with computer F
Answers
Answer:
To reach best results:
Break down all connections.
What standards organization maintains the ethernet standard?.
Answers
Answer:
Ethernet standards are written and maintained by the IEEE, the Institute of Electrical and Electronic Engineers which has its corporate office in New York City and its operations center in Piscataway, New Jersey.
Explanation:
Do you have any sprites for Friday Night Funkin?
I am making mods and any sprites you have are fine. They just need to follow the idle rule and be appropriate :)
Answers
Answer:
id.k t
Explanation:
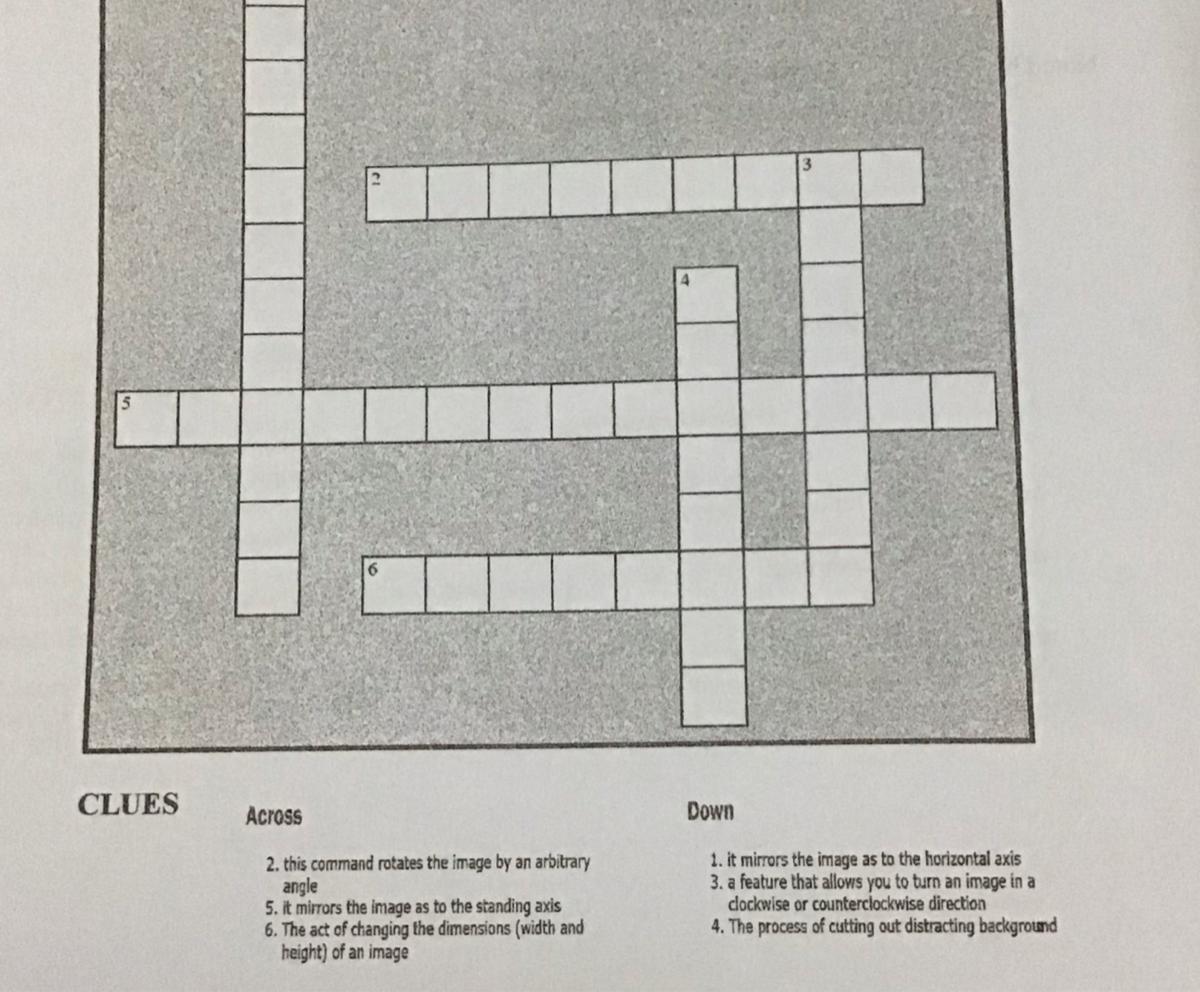
Answer this crossword for brainliest and 15 points
Answers
Answer:
I like ur cut G
Explanation: